The need for online security and anonymity is ever-growing. Corporations are tracking our every step for ad revenue, while hackers and other bad actors are looking for other ways to trick us into getting our data. But when there’s a need, there’s a way.
The Dolphin browser provides exactly that – a way to ensure your anonymity and security online. It hasn’t become widespread yet just because it requires some additional tools, namely proxies, and know-how to set up it properly. I’m here to fill in this knowledge gap.
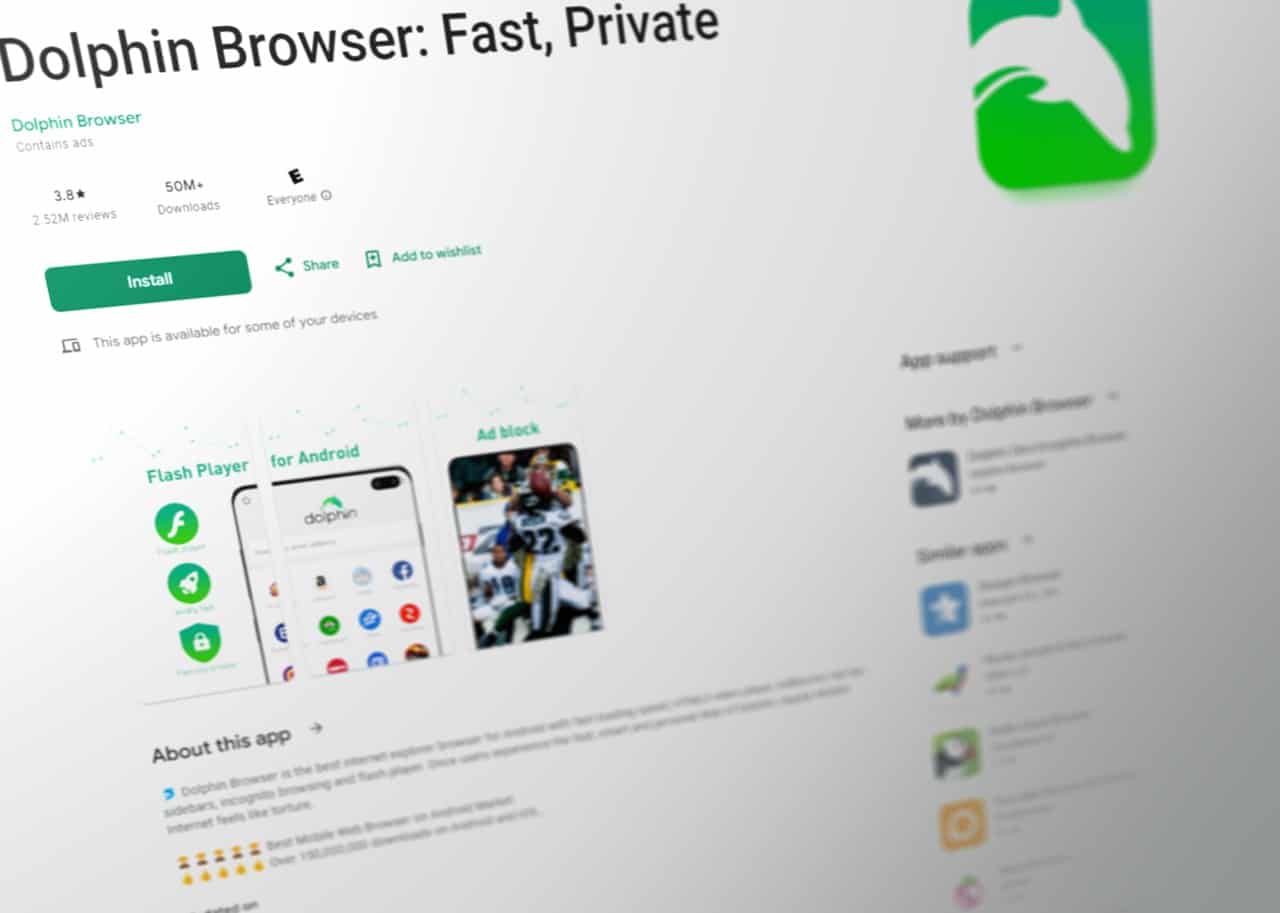
? Dolphin Browser is the best internet explorer browser for Android with fast loading speed, HTML5 video player, AdBlocker, tab bar, sidebars, incognito browsing and flash player. Once users experience the fast, smart and personal Web of Dolphin, regular Mobile Internet feels like torture.
https://play.google.com/store/apps/details?id=mobi.mgeek.TunnyBrowser
Fingerprints and the Dolphin Browser
Whenever you enter a website, it collects all sorts of data about you. IP address, browser and operating system version, screen resolution, and sometimes your hardware parameters. This bundle of data is called a digital fingerprint.
Just like a regular fingerprint, it is used for identification purposes. But online fingerprints are even worse. They can be used to constantly track what you are doing online. An incognito mode does not help since common browsers still leave a mark.
Dolphine Anty browser is an anti-detect browser that can help you hide your fingerprint and even simulate a needed profile. There are other browsers that can achieve similar results, for example, Tor, but Dolphin has an advantage in one area.
It’s optimized for affiliate marketing and traffic arbitrage purposes. Simply put, it helps media buyers to access multiple social media accounts. Dolphin is crucial for automating various social media management tasks and sharing access between teams.
It works by allowing users to create various fingerprint profiles – combinations of factors of browsers, OS versions, screen resolutions, etc. While a common browser sends its identifying information to the website server, Dolphin is programmed to send only the information you set up in the profile.
Benefits of the Dolphin Browser
Besides affiliate marketers, the Dolphin browser can also be used for anonymity purposes. The websites you visit will have a more difficult time tracking what you are doing if you switch your fingerprint profiles.
The Dolphin browser is also commonly used by cybersecurity experts or anti-fraud teams to test networks and software. Changing the fingerprint profiles is crucial for such testing but requires time and resources. Dolphin saves both.
But all of these use cases are also applicable to other anti-detect browsers. Dolphin has some benefits over other anti-detect browsers specifically.
- User interface. Dolphin largely looks like a common browser, designed to look similar to Chrome. It also flawlessly works on iOS and Android devices.
- Fingerprinting options. Anti-detect browsers tend to lack some functions and excel at others. Dolphin supports all that matters – WebGL, timezone, Canvas, geolocation, and other fingerprint parts.
- Teamwork capabilities. Perhaps most importantly, Dolphin is designed to be used by teams. The created profiles can be shared between devices, while activity and account statuses are visible to everyone.
Why Are Proxies Essential for Dolphin?
The Dolphin software allows you to change various browsers, operating systems, and hardware parameters when setting up the fingerprint profile. They all significantly benefit your anonymity online, but alone are insufficient.
IP address is the single most important parameter by which websites identify and track users. It is a string of numbers and letters assigned by your internet service provider to a location. This location can even be neighborhood-accurate.
Even if you set up Canvas fingerprint to show a different combination of browsers, operating systems, and PNG headers each time you log in, the website will know you from your IP address.
It is one of the first things websites check when screening visitors as geo-restrictions and various website parameters, such as language, are set according to the IP. In fact, many websites do not even use other fingerprinting techniques.
We can think of IP addresses as the basis for identification. When it doesn’t align with other fingerprint parts, you appear more suspicious. Fortunately, setting up proxies in the Dolphin browser is not that difficult.
How To Set Up Proxies for Dolphin
The first step is, obviously, to get proxies. I do not recommend using free proxies as they might track you or provide poor performance. But even between paid proxy providers, some are better with anti-detect browsers than others.
A good idea is to read about the particular proxy provider you want to use. Some providers great with privacy browsers have even set up their own Dolphin proxy tutorials. Following them is the most hassle-free method of setting up Dolphine. The usual steps they all include are these,
- If you haven’t already, download the Dolphin{Anty} web browser from here and sign up.
- After installing the browser, you will need to sign in with your account.
- At the top, you will see a “create profile” button. Press on it.
- Then, you will be able to add various fingerprint settings. For adding a proxy, only the name of the profile is enough.
- Between all the settings, you will see the choices of “no proxy,” “new proxy,” or “saved proxies.” You should choose to add a new one or select “saved proxies” to see your list.
- Below, you will be able to add the proxy IP address and port number. You will need to enter them separated by a colon. For example, 110.14. 56.19:8008. Contact your provider for instructions on where to find your proxy credentials. Proxy name and other parameters are options.
- Check for connection by pressing the button on the right text box. If Dolphin does not give you any errors, your proxies are ready to go!
- Don’t forget to press the “new fingerprint” and “create” buttons on the top right.
Setting Up a Dolphin Proxy Is a Simple
There you have it! Setting up a Dolphin proxy is a simple process. While it’s easy to start using Dolphin, it might take time for you to perfect your fingerprint settings for maximum anonymity. But setting up a proxy server correctly is the first step in the right direction.